Cybercriminals are always looking for new ways to steal credentials and gain access to systems. A recent attack highlights just how deceptive these tactics can be. This method involves tricking users into bypassing security protections by manipulating CAPTCHA verification steps.
Why Your Credentials Matter
Your online credentials—usernames, passwords, and multi-factor authentication (MFA) tokens—are valuable to criminals. They use stolen login information to:
- Access bank accounts and steal money
- Compromise business systems for fraud and ransomware
- Sell credentials on the dark web for other criminals to exploit
- Use your identity for further attacks, including phishing or social engineering
Because of this, cybercriminals are always refining their methods to trick users into giving up their credentials or installing malware.
The Site Compromise
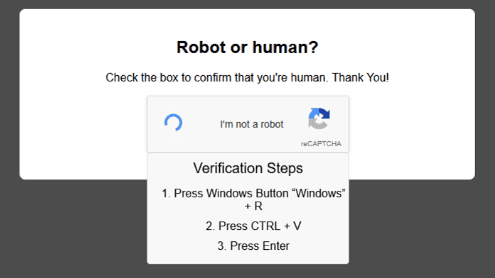
This recent attack started with a website compromise. The popular site HEP2go was breached, and attackers modified it to display a fake reCAPTCHA verification prompt. Users were asked to complete a CAPTCHA, which is a common security feature designed to distinguish humans from bots.
However, instead of a normal CAPTCHA challenge, users were given additional instructions:
- Press Windows + R to open the Run dialog box
- Paste the provided text
- Press Enter
Unknowingly, users who followed these steps were running malicious code that installed an info-stealer—a type of malware designed to collect saved passwords, browser cookies, and other sensitive information.
How the Attack Works
This attack is effective because it leverages a mix of social engineering and system functionality:
- Users trust CAPTCHAs – Since CAPTCHAs are used to verify human users, most people don’t question their legitimacy.
- The Run command executes code – The Windows Run dialog allows users to quickly open programs or execute commands, making it an easy target for abuse.
- Malware runs in the background – Once installed, the info-stealer quietly gathers and exfiltrates sensitive data without the user noticing.
How to Protect Yourself
To avoid falling victim to similar attacks, follow these security practices:
- Never follow unexpected instructions from a website
- No legitimate CAPTCHA system will ask you to run commands on your computer.
- Be skeptical of unusual verification steps
- If a CAPTCHA asks for more than clicking a checkbox or selecting images, stop and investigate.
- Use a password manager
- Storing passwords in a password manager prevents malware from easily stealing saved credentials.
- Keep your software and antivirus updated
- Security updates patch vulnerabilities that malware exploits.
- Enable multi-factor authentication (MFA)
- Even if a password is stolen, MFA adds an extra layer of security.
- Monitor your accounts for unusual activity
- Check login histories and set up alerts for new sign-ins.
- Report suspicious sites
- If you encounter a phishing site, report it to your security team or browser security features.
Final Thoughts
This attack is a reminder that cybercriminals are always finding new ways to bypass security measures. Staying aware of these tactics and practicing good security hygiene can help keep your credentials—and your systems—safe.